The TAS Security Node’s research is centred around a seamless collaboration between fundamental cross-disciplinary security research and autonomous systems research at Lancaster and Cranfield Universities. To accomplish this vision, TAS-S utilizes interlinked cross disciplinary Research Strands (RS) to address 3 core challenge areas in autonomous system (AS) security. The following image below shows the interconnectivity of the research strands, further details of which can be found in the dedicated sections below.
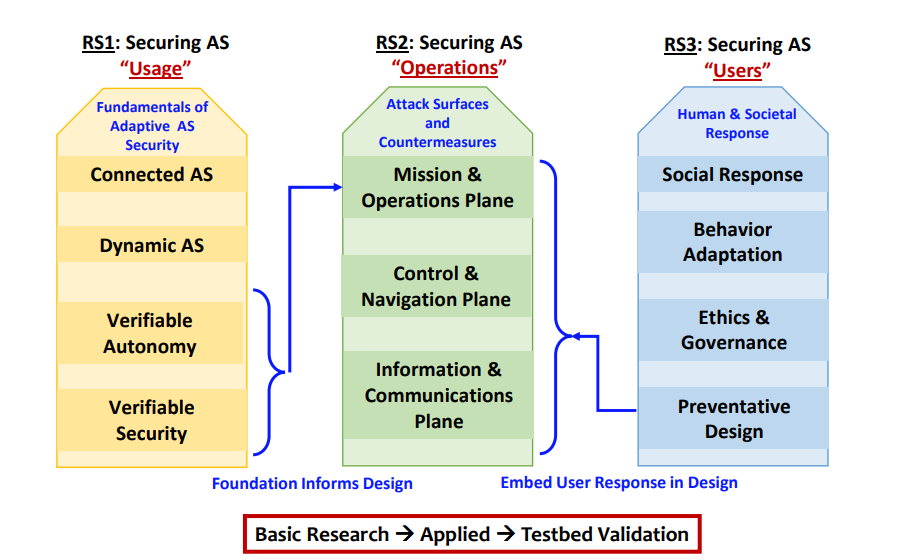
RS1: Can we secure the AS “Usage” environment? Lead: N. Suri
To establish the fundamental AS “usage” framework for providing and assessing multi-layered, multi- dimensional adaptive AS security in dynamic mixed mode environments.
- Theme A: Dynamic and Compositional AS Security (Lead: N. Suri, Participants: A. Tsourdos, G. Inalhan , A. Sogokon).
- Theme B: Explainable and Verifiable Decision Making for AS Security (Lead: P. Angelov, Participants: N. Suri, W. Guo, G. Inalhan, Z. Yu, A. Sogokon, E. Almeida Soares)
Further details can be found on the dedicated RS1 webpage.
RS2: Can we secure the AS “Operations” environment? Lead: W. Guo
To ascertain exposure (and their consequent mitigation) of AS “operations” to cyber-physical attacks by characterizing the attack surfaces (i.e., entry points and likelihoods) across the mission, control and information surfaces in a technology and mission-invariant manner.
- Theme A: Security in the Mission and Operational Surface (Leads: P. Angelov, Participants: A. Tsourdos, Z. Yu, E. Almeida Soares, O. Gonzalez Villarreal)
- Theme B: Securing the Control Surface (Lead: G. Inalhan, Participants: P. Angelov, A. Tsourdos, B. Yuksek)
- Theme C: Securing the Cross-Layer Networking Surface (Communication, Sensors) (Lead: W. Guo, Participants: D. Hutchison, D. Prince, P. Ciholas, Z. Wei)
RS3: Can we secure the AS “User” environment? Lead: C. May-Chahal
To ascertain the overall AS threats across multiple attacks, or approach tackles three interdependent AS surfaces (mission, control and communication) while the security foundations of RS1 and the human behaviour from RS3 are used to create holistic mitigation strategies.
- Theme A: Behaviour Adaptation as a Basis of Security by Design (Lead: L. Dorn, Participant: J. Deville.)
- Theme B: Organisational Socio-Technical Mitigation (Lead: J. Deville, Participants: L. Dorn, C. May-Chahal, L. Moffatt).
- Theme C: Ethics and Governance of AS Security (Lead: C. Easton, Participants: L. Dorn, L. Moffatt,)
Further details about the three themes above, plus our collaboration with National Highways, can be found on the dedicated RS3 webpage.
Further information about the TAS-S project can be found here.